In response to market and competitive forces, many companies have turned their attention to developing higher quality and more secure software. Whether that software is their product or is a component of their product, quality and especially security have become required vs optional. To accommodate the security requirements, some companies have adopted DecSecOps overlays to their software development process that can and has caused significant disruption to their process. This blog series is aimed at helping to understand how the transition to DevSecOps need not be traumatic and that a cautious approach that leverages state of the art tools and techniques can be helpful. Consider this blog series a practical approach to DevSecOps.
This post discusses a practical approach to transition to DevSecOps by transitioning your focus on security to earlier in the development lifecycle. Click here for the other posts in the series.
Integrating SAST and SCA into the Existing Workflows
There are two important considerations when adding security to existing DevOps pipeline. The first is security in code, which means, when code is developed, the security of the code itself should be continuously reviewed and assessed. The second is security as code, in other words, security requirements need to be part of the process from the beginning. Let’s look at both of these concepts in a bit more detail.
Security in Code
Many teams start their path to security off by adopting coding guidelines or standards such as MISRA, or the CERT guidelines, which is a great start, it improves code security from the get-go. However, just following a coding standard by itself does not necessarily avoid complex security vulnerabilities. According to a recent study by Microsoft, 70% of today’s security vulnerabilities are caused by memory access errors. Memory vulnerabilities here could be caused by a simple miscalculation, which led to a buffer-overrun-write, or a more complex path where a variable is tainted through input from the outside that is used without being sanitized. To find these problems in the code, more sophisticated analysis is needed such as dataflow analysis and abstract execution provided by advanced tools like GrammaTech CodeSonar.
Equally important is understanding the security implications of the software your products depend on such as open source, internal reused code and commercial software. Without this, your best efforts will be for naught if vulnerabilities exist in third-party code included in your application. SCA tools such as GrammaTech CodeSentry provide a continuous software bill of materials (SBOM) that itemizes all the software libraries in your dependencies and associated known vulnerabilities. This SBOM is established early on in development is updated continuously as dependencies evolve both from updates and newly discovered vulnerabilities.
Security as Code
An interesting approach that has come out of DevSecOps practice is the concept of treating security in the same ways as code is; guided by requirements, which leads to implementation of security controls, then to validation through testing, and of course, documentation. It’s one of the key ways to integrate security into DevOps and a good way to build security into the development culture and have software teams communicate using a familiar language. Certainly, security implementations that end up as actual code with associated tests can be automated in the same fashion as other code. Automation tools apply here as would any tool that works with requirements, tests, documentation, etc.
Each iteration through a continuous process requires a review which includes the backlog of security issues but also important data on changes needed to security controls and requirements. This feedback into the process is key and important part of making DevSecOps success – repeat, review and refine. The following diagram show how the results of the review stage update and feedback into the next cycle.
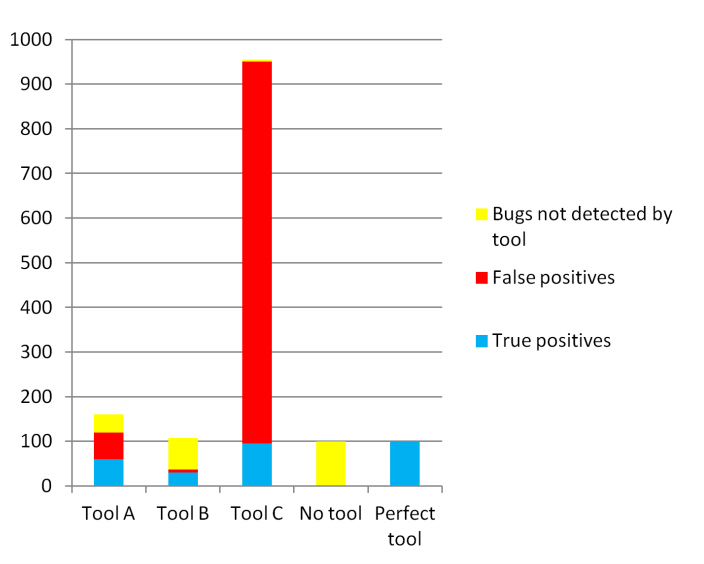
Figure 1: DevSecOps requires security requirements, controls and coding standards fed into each part of the pipeline. Importantly, feedback is required to close the loop.
Integrating SAST and SCA to Shift Left Security
Automation is one of the main tenants of DevOps. Nothing should be dependent on manual steps as they can be easily overlooked, either by accident or by malicious intent. SCA tools can be used immediately to establish a baseline SBOM for the application. Without first understanding the vulnerabilities and risks associated with your software stack, other measures will be in vain. It’s equally important to keep this SBOM up-to-date with each iteration since the threat landscape can change over time as does the composition of the dependencies. GrammaTech CodeSentry analyzes third-party binaries so even if source isn’t available, your exposure is manageable.
SAST is used as soon as code is available in a project and automates the coding compliance and automatic detection of defects and vulnerabilities. In fact, as soon as it’s been typed in by a developer – the sooner the better. CodeSonar integrates with popular IDEs and provides immediate feedback on newly developed code, before it gets committed to the source repository.
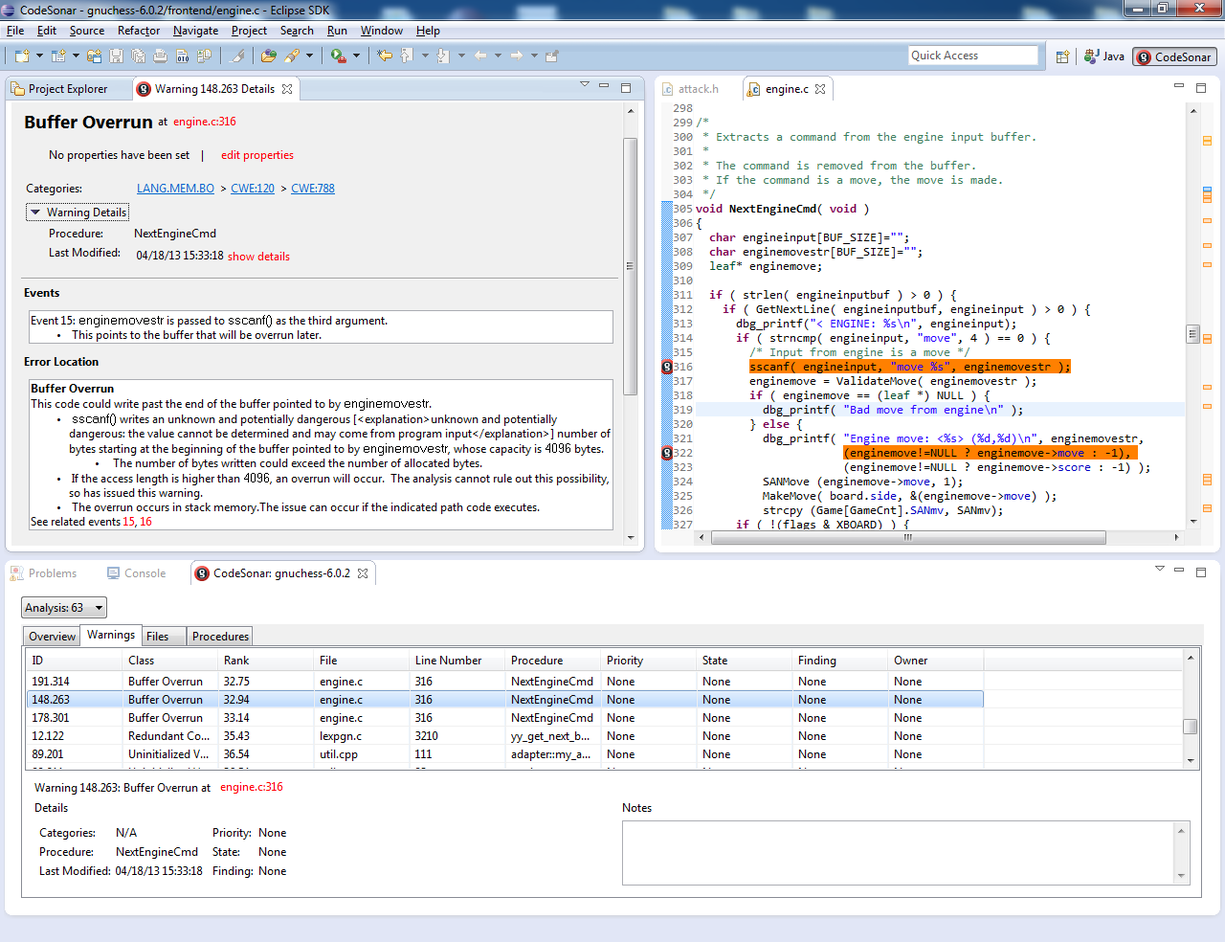
Figure 2: An example warning generate by CodeSonar within Eclipse. Error messages are accompanied with detailed description and trace information highlighted in the source code.
SAST come in all types of shapes and sizes, some focus on coding standards, some, more advanced tools, step beyond the coding standards and explore data flow, control flow and abstract execution techniques to find defects in the source code that arise from programming or logic mistakes. CodeSonar helps achieve security in code and assist in creating security as code – one tool that covers coding standards, security control enforcement and vulnerability detection.
Continuous integration and deployment processes rely on automation to realize their promised benefits. Without efficient progress through the cycle, the continuous nature of the processes amplifies inefficiencies. All new code has vulnerabilities, the challenge teams face is to remove these as early as possible with as little effort as possible. SCA ensure the software stack is secure while SAST improves custom code security and quality early in the process and helps developers do this as easily as possible, ideally, integrated into their development environment.
Summary
SAST and SCA tools are an important part of shifting security left because they are used immediately at the early stages of a project. They are also instrumental in helping enforce security controls and coding standards required for the application meanwhile detecting new, possibly complex, security vulnerabilities as they arise. SCA tools ensure the software stack is accounted for with a software bill of materials that show both contents and existing security vulnerabilities in your software dependencies. Over time, these tools are part of the regular part of the team’s workflow providing better code but critical data on general progress.
The move to integrating security into an existing DevOps pipeline starts with introducing best practices early in the development lifecycle. SCA and SAST tools are ideal for facilitating this transition. In addition, the feedback to developers and management is crucial in both improving security and the critical feedback it provides, improves the process in general.